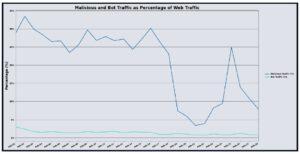
March brought a significant pullback in raw traffic volume across DigiCert’s UltraWAF infrastructure, with the platform processing just over 1.4 billion web requests, a 26.82% decrease from February. Malicious traffic fell even more sharply, dropping 72.76% month over month to roughly 121 million requests, or 8.37% of all observed traffic. Bot violations followed a similar trajectory, declining 38.94% to approximately 17 million, accounting for 1.22% of total web traffic. The combined reduction across all three categories suggests the outsized February figures were in part driven by temporary campaign activity that did not sustain into March, rather than a structural increase in baseline threat volume.
Despite the overall decline, the composition of malicious traffic in March reinforced patterns worth monitoring. Cookie-related attacks remained the dominant threat category at 52.90% of all malicious traffic, with Command Injection following at 35.00%, a notably elevated share compared to prior months. The most pronounced movement came from Buffer Overflow activity across two detection categories, with Buffer Overflow Cookie increasing 93.96% over February and Buffer Overflow Header detections compounding the trend, both pointing to malicious actors favoring memory corruption techniques over conventional web injection, targeting low-level parsing logic in native server components and compiled application modules rather than application code directly.
The Financial sector observed the largest share of targeted traffic in March, accounting for 64.71% of all malicious requests, with Travel and Hospitality second at 15.81% and Government third at 13.41%. The concentration in Financial is consistent with sustained automated targeting of high-value transaction infrastructure and is not unusual for the quarter, given that tax season drives elevated activity across financial platforms and creates conditions where legitimate traffic spikes can be used to mask probing.
The observed payloads this month reflected a threat environment oriented heavily toward credential access, persistent execution, and infrastructure fingerprinting. Several requests targeted exposed developer toolchain artifacts, including attempts to retrieve .claude/.credentials.json files associated with Anthropic’s local AI tooling, placing AI-adjacent credential targets alongside the established sweeps for AWS, Azure, and GCP credential files that continue to appear consistently. More technically aggressive payloads included a Spring4Shell exploit using ${IFS} substitution to bypass space-based WAF rules combined with a UDP out-of-band callback for silent RCE confirmation, and a Log4Shell variant that reconstructed the jndi:ldap: string character by character using nested Log4j lookup expressions to evade signature detection entirely. QNAP NAS devices were targeted via the messagebus unauthenticated CGI path, with base64-encoded dropper commands pulling from the same C2 infrastructure observed in multiple payloads, suggesting a coordinated campaign rather than independent scanning. XWiki installations were probed for Groovy template injection via the SolrSearch endpoint, while TP-Link routers were targeted through the LuCI session token bypass. Across the full payload set, the recurring themes are exploitation of development infrastructure left exposed in production, multi-layer evasion designed to defeat signature-based detection, and out-of-band confirmation techniques that validate execution without generating obvious log artifacts.
March’s data tells a more nuanced story than the volume decline alone suggests. Raw request counts fell sharply, but the payloads observed during the month were technically deliberate, with multiple attempts combining evasion layering, out-of-band execution confirmation, and coordinated dropper infrastructure across different vulnerability classes. The sustained pressure against credential files, developer tooling artifacts, and embedded device management interfaces reflects targeting behavior that does not scale down with traffic volume. What the month ultimately demonstrates is that lower traffic is not the same as lower risk, and the sophistication concentrated in a smaller payload set can carry more operational consequence than a high-volume month dominated by generic scanning noise.
Stats at a Glance
- Total Web Requests: 1,448,752,629
- Largest Threat Category: Cookie (52.90%)
- Total WAF Violations: 121,240,053
- Top Three Industry Targeted: Financial (43.40%), Travel/Hospitality (15.81%), Government (13.41%)
- Total Bot Violations: 17,614,017
- Top Three Source Countries: United States (43.40%), Great Britain (13.93%), Germany (2.14)